CISO as a Service
Whitepaper: Building Resilience with the Right Strategy: Setting Up IT Security Effectively
A guide to creating lasting security
Read now
Expertise in Information Security at Your Service
Our certified experts possess extensive knowledge to guide you through every step of the audit process, identify potential risks, and implement preventive measures. We deliver practical solutions for effective risk management, swift incident response, and the enhancement of your business continuity management. This ensures that your IT security remains current and that you successfully meet your compliance objectives.
Certified ISO 27001 Auditors: Our certified ISO 27001 auditors are experts who understand precisely what to prioritize during the (re-)certification process.
Experience in IT Project Implementation: We bring practical expertise from a wide range of successfully completed IT projects.
Technical Language Competence: We bridge the gap between Governance, Risk & Compliance (GRC) and IT engineering, ensuring comprehensive coverage of all relevant areas.
Maintaining Certification Through Continuous Improvement and Risk Management
To maintain certification, merely preserving the status quo is insufficient. External auditors typically offer recommendations or highlight discrepancies that must be addressed. An internal audit, as explicitly required by ISO 27001, is essential for fostering continuous improvement and identifying emerging risks.
Our CISO-as-a-Service (CISOaaS) guides you through this process by managing your Information Security Management System (ISMS), identifying new risks, and effectively preparing your employees for the next external audit. This approach ensures that you remain compliant and well-prepared at all times.
Rapid and Effective Response in the Event of an Attack
CISOaaS should not be confused with an incident retainer, which provides resources quickly during emergencies. While a retainer focuses primarily on immediate assistance, CISOaaS not only supports critical actions during an incident but also coordinates communication with authorities to ensure compliance with reporting obligations.
The key advantage of CISOaaS lies in proactive preparation. We ensure that a clear emergency plan is established, processes are rehearsed collaboratively, and the restoration of normal operations occurs quickly and smoothly.
Optimierung Ihres Business Continuity Managements (BCM)
CISOaaS evaluates and enhances your Business Continuity Management (BCM) through practical exercises, ensuring that your emergency plan is robust and adaptable to various scenarios. We identify and address gaps or misunderstandings early on, promoting a well-developed and effective BCM.
Effective Risk Management Through CISOaaS
CISO-as-a-Service (CISOaaS) oversees and manages risk management for information security. Acceptance criteria and risk appetite are determined by executive management or the board of directors. Specific risks are assessed by relevant stakeholders with the necessary expertise, with CISOaaS providing support as needed.
Our CISOaaS compiles and evaluates the results of risk assessments and develops a prioritized action plan, which is then submitted to management for approval.
Support in Implementing and Maintaining an ISMS
Before engaging with a CISOaaS, an Information Security Management System (ISMS) should already be established and actively utilized. We are here to support you in developing your own ISMS through an implementation program up to audit readiness, after which we can take over the ongoing maintenance of the ISMS through CISOaaS.
Conclusion on BNC's CISOaaS
With our CISOaaS, you benefit from an experienced team dedicated to helping you maintain your ISO 27001 certification while continuously optimizing your security strategy. Our certified ISO 27001 auditors know precisely what to focus on during (re)certification, and we provide practical expertise drawn from numerous successfully completed IT projects.Our proficiency in Governance, Risk, and Compliance (GRC) and IT engineering ensures comprehensive coverage of all relevant security aspects. We deliver pragmatic, actionable solutions that genuinely advance your organization. Whether you need assistance in preparing for your next audit, optimizing risk management, or enhancing your Business Continuity Management (BCM), our CISOaaS offers comprehensive and proactive support to sustainably strengthen your IT security.

ISO 27001 Self-Assessment
Evaluate potential vulnerabilities and areas for improvement in your organization:
Start your free self-assessment now!
FAQ CISO as a Service
-
When is a CISOaaS offering the right choice for our company?
There are various reasons why it may be preferable to utilize a CISO as a Service rather than hiring a full-time CISO. These include, among others:
- You have not yet found a qualified CISO of your own or need to bridge a gap in staffing.
- You are not yet able to adequately assess candidates and require more experience regarding what a CISO should do and be capable of in your organization.
- There is not enough work to justify a full-time position.
- You plan to take on this role yourself in the medium term but need support during the transition period.
There are various reasons why it may be preferable to utilize a CISO as a Service rather than hiring a full-time CISO. These include, among others:
- You have not yet found a qualified CISO of your own or need to bridge a gap in staffing.
- You are not yet able to adequately assess candidates and require more experience regarding what a CISO should do and be capable of in your organization.
- There is not enough work to justify a full-time position.
- You plan to take on this role yourself in the medium term but need support during the transition period.
-
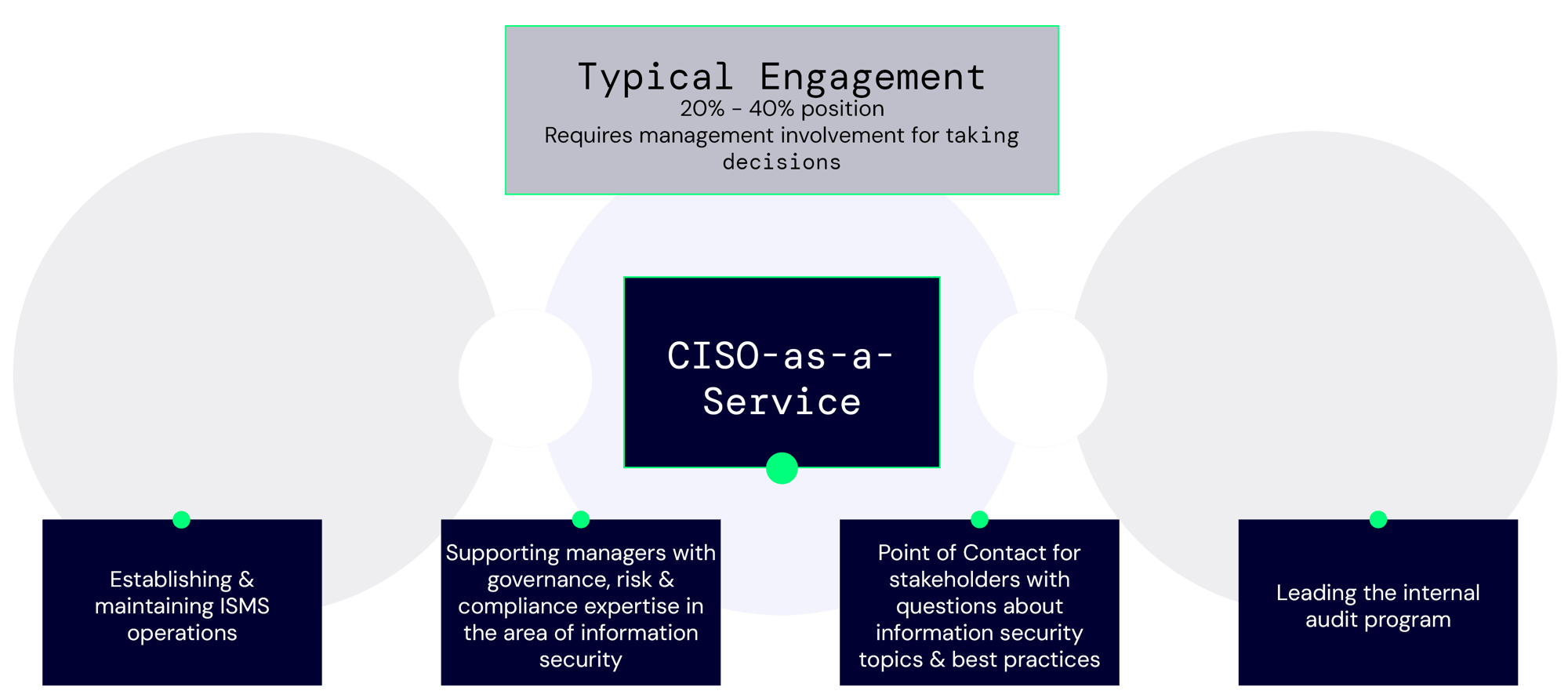
What does a CISOaaS engagement look like?
Depending on the workload, we provide you with a dedicated, qualified individual who typically works 1 to 2 fixed days per week. During this time, the ISMS is maintained, questions are answered, and decisions are prepared.
Ideally, our Information Security Consultant works closely with one of your leadership team members, actively sharing knowledge and providing the necessary support to continuously improve information security in your organization. -
Can a CISOaaS replace a departing CISO?
Depending on the workload, a CISOaaS can temporarily fill a vacancy in your organization or even serve as a long-term replacement.
-
What can we delegate to a CISOaaS?
An Information Security Consultant in a CISOaaS engagement will help you further develop the ISMS and make the right decisions. However, they cannot fulfill all information security tasks without the collaboration of all departments. The accountability for decisions always remains with the commissioning organization. We assist you in understanding the requirements, potential consequences, and alternatives, as well as in justifying and communicating the decisions.
-
What are the daily tasks of a CISO?
A CISO is primarily responsible for maintaining and managing an ISMS. This involves various metrics and self-set goals that need to be achieved.
To this end, the CISO will monitor progress, suggest improvements, serve as a point of contact, and coordinate the work of different departments to ensure consistent implementation of security policies. In special events such as security incidents, they can take a leading role in the aftermath. Thus, they primarily assume an organizational and coordinating role, with extensive expertise in information security and risk assessment. However, ultimately, there is no typical daily routine in the life of a CISO.
